CVE-2026-22679
Weaver E-cology 10.0 Unauthenticated RCE via dubboApi Debug Endpoint
Description
Weaver (Fanwei) E-cology 10.0 versions prior to 20260312 contain an unauthenticated remote code execution vulnerability in the /papi/esearch/data/devops/dubboApi/debug/method endpoint that allows attackers to execute arbitrary commands by invoking exposed debug functionality. Attackers can craft POST requests with attacker-controlled interfaceName and methodName parameters to reach command-execution helpers and achieve arbitrary command execution on the system. Exploitation evidence was first observed by the Shadowserver Foundation on 2026-03-31 (UTC).
INFO
Published Date :
April 7, 2026, 1:16 p.m.
Last Modified :
May 5, 2026, 2:16 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | 83251b91-4cc7-4094-a5c7-464a1b83ea10 | ||||
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 4.0 | CRITICAL | 83251b91-4cc7-4094-a5c7-464a1b83ea10 | ||||
| CVSS 4.0 | CRITICAL | [email protected] |
Solution
- Update Weaver E-cology to version 20260312 or later.
- Disable or restrict access to the /papi/esearch/data/devops/dubboApi/debug/method endpoint.
- Review and secure all exposed debug functionalities.
Public PoC/Exploit Available at Github
CVE-2026-22679 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2026-22679.
| URL | Resource |
|---|---|
| https://h4cker.zip/post/d5d211/ | Broken Link |
| https://ti.qianxin.com/vulnerability/notice-detail/1760 | Third Party Advisory |
| https://www.vulncheck.com/advisories/weaver-e-cology-unauthenticated-rce-via-dubboapi-debug-endpoint | Third Party Advisory |
| https://www.weaver.com.cn/cs/securityDownload.html# | Patch |
| https://blog.vega.io/posts/cve-2026-22679-weaver-ecology-exploitation/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2026-22679 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2026-22679
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Critical RCE vulnerability (CVSS 9.3) in Weaver E-cology platform versions prior to build 20260312. Unauthenticated remote code execution via exposed debug endpoint at /papi/esearch/data/devops/dubboApi/debug/method. Comprehensive analysis, proof-of-concept, and detection guidance included.
cve cybersecurity java rce unauthenticated vulnerability-research weaver ecology-oa enterprise-oa
Python Lua
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2026-22679 vulnerability anywhere in the article.

-
CybersecurityNews
Critical Weaver E-cology RCE Vulnerability Actively Exploited in Attacks
A critical unauthenticated remote code execution vulnerability in the Weaver E-cology platform is currently being actively exploited in the wild. CVE-2026-22679 carries a maximum CVSS score of 9.8 and ... Read more

-
The Hacker News
Weaver E-cology RCE Flaw CVE-2026-22679 Actively Exploited via Debug API
A critical security vulnerability in Weaver (Fanwei) E-cology, an enterprise office automation (OA) and collaboration platform, has come under active exploitation in the wild. The vulnerability (CVE-2 ... Read more

-
Daily CyberSecurity
Critical 9.8 CVSS Flaws Hit ArcGIS Infrastructure
Esri has issued an urgent security bulletin regarding two critical vulnerabilities affecting developer credentials within ArcGIS Online, ArcGIS Location Platform, and ArcGIS Enterprise. The flaws, whi ... Read more

-
Daily CyberSecurity
In the Wild: Information Disclosure (CVE-2026-20133) Exploited in Cisco SD-WAN Manager
The networking giant Cisco has issued an urgent warning to enterprise administrators. In April 2026, the Cisco Product Security Incident Response Team (PSIRT) confirmed they are aware of active exploi ... Read more
-
Daily CyberSecurity
Linux Privilege Escalation: “Pack2TheRoot” Flaw Impacts Major Distributions
A long-standing security flaw has been unearthed in a core component of the modern Linux desktop and server ecosystem. Known as Pack2TheRoot, this critical vulnerability resides in PackageKit, a D-Bus ... Read more

-
Daily CyberSecurity
Over 400,000 WordPress Sites at Risk as “Breeze” Plugin Zero-Day Is Exploited in the Wild
A major security threat is currently sweeping through the WordPress ecosystem. Breeze, a highly popular caching plugin developed by the Cloudways team and active on over 400,000 websites, is under act ... Read more

-
Daily CyberSecurity
CVE-2026-33626: High-Severity SSRF Exploited in the Wild to Hijack AI Inference Engines
On April 21, 2026, a high-severity Server-Side Request Forgery (SSRF) vulnerability was disclosed in LMDeploy, a popular toolkit for serving vision-language and large language models (LLMs). Within a ... Read more

-
Daily CyberSecurity
Microsoft Defender Zero-Day “BlueHammer” Hits KEV Catalog Following Researcher’s Protest
Image: Will Dormann CISA has officially added a fresh vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, citing evidence of active exploitation in the wild. The flaw, tracked as CVE-2 ... Read more

-
Daily CyberSecurity
GitLab Security Update: High-Severity Vulnerabilities Patched in April Release
GitLab has released a vital set of security updates for both Community Edition (CE) and Enterprise Edition (EE) to address a range of vulnerabilities, including high-severity flaws that could allow un ... Read more

-
Daily CyberSecurity
CVE-2026-40342: CVSS 10.0 Path Traversal to RCE in Firebird Database
Researchers have disclosed a critical-severity vulnerability in Firebird, the long-standing relational database with roots dating back to 1981, that allows attackers to execute arbitrary code with the ... Read more

-
Daily CyberSecurity
Command Injection Vulnerability (CVE-2025-29635) Exploited in the Wild
The Akamai Security Intelligence and Response Team (SIRT) has issued a warning regarding a surge in malicious activity targeting end-of-life networking hardware. According to a new report, threat acto ... Read more

-
Daily CyberSecurity
Critical RCE Alert: Bamboo Data Center Vulnerable to OS Command Injection
Atlassian has issued a high-priority advisory for its Bamboo Data Center users, detailing a critical-severity security flaw that could allow attackers to take full control of affected servers. The vul ... Read more
-
Daily CyberSecurity
Three Silent Vulnerabilities Discovered in the glibc Core
The core of many Linux-based operating systems is facing a series of security challenges. Recent advisories for the GNU C Library (glibc) have disclosed three distinct vulnerabilities ranging from hea ... Read more

-
Daily CyberSecurity
The Dual CVSS 10.0 RCE Flaws Threatening Spinnaker Pipelines
A pair of critical remote code execution (RCE) vulnerabilities has been disclosed in Spinnaker, the heavyweight open-source platform used by tech giants like Adobe, Airbnb, and JPMorgan Chase to manag ... Read more

-
Daily CyberSecurity
Critical 9.8 RCE Threat to SGLang AI Infrastructure
A critical remote code execution (RCE) vulnerability has been uncovered in SGLang, a popular open-source framework used to serve advanced models like DeepSeek and Mistral. The flaw, officially tracked ... Read more

-
Daily CyberSecurity
MOVEit WAF Critical Alert: Multi-Level RCE and WAF Bypass Vulnerabilities Disclosed
Progress Software has released a critical security bulletin for April 2026, revealing five high-impact vulnerabilities affecting MOVEit WAF and related Application Delivery Controller (ADC) products. ... Read more
-
Daily CyberSecurity
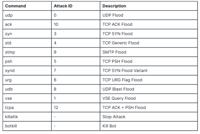
Nexcorium Botnet Turns Unpatched DVRs into DDoS Foot Soldiers
Security researchers at FortiGuard Labs have uncovered a sophisticated campaign deploying Nexcorium, a multi-architecture Mirai variant that turns unpatched digital video recorders (DVRs) into foot so ... Read more

-
Daily CyberSecurity
CISA Warns of Active Exploitation in Cisco, PaperCut, and Zimbra
The Cybersecurity and Infrastructure Security Agency (CISA) has expanded its Known Exploited Vulnerabilities (KEV) Catalog, adding eight high-impact flaws. The update comes following confirmed evidenc ... Read more

-
Daily CyberSecurity
Progress Kemp LoadMaster Alert: Multiple RCE and WAF Bypass Flaws Patched
The Progress Kemp LoadMaster team has confirmed a significant security event involving five high-severity vulnerabilities affecting its application delivery controllers. These flaws, which impact both ... Read more

-
Daily CyberSecurity
ASUSTOR Issues Critical Patch: Command Injection Vulnerability Threatens ADM Users
ASUSTOR has issued an urgent security advisory regarding a high-severity command injection vulnerability impacting its ASUSTOR Data Master (ADM) operating system. Identified as CVE-2026-6644, this fla ... Read more
The following table lists the changes that have been made to the
CVE-2026-22679 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
May. 05, 2026
Action Type Old Value New Value Added Reference https://blog.vega.io/posts/cve-2026-22679-weaver-ecology-exploitation/ -
Initial Analysis by [email protected]
Apr. 24, 2026
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:weaver:e-cology:*:*:*:*:*:*:*:* versions up to (excluding) 20260312 Added Reference Type VulnCheck: https://h4cker.zip/post/d5d211/ Types: Broken Link Added Reference Type VulnCheck: https://ti.qianxin.com/vulnerability/notice-detail/1760 Types: Third Party Advisory Added Reference Type VulnCheck: https://www.vulncheck.com/advisories/weaver-e-cology-unauthenticated-rce-via-dubboapi-debug-endpoint Types: Third Party Advisory Added Reference Type VulnCheck: https://www.weaver.com.cn/cs/securityDownload.html# Types: Patch -
New CVE Received by [email protected]
Apr. 07, 2026
Action Type Old Value New Value Added Description Weaver (Fanwei) E-cology 10.0 versions prior to 20260312 contain an unauthenticated remote code execution vulnerability in the /papi/esearch/data/devops/dubboApi/debug/method endpoint that allows attackers to execute arbitrary commands by invoking exposed debug functionality. Attackers can craft POST requests with attacker-controlled interfaceName and methodName parameters to reach command-execution helpers and achieve arbitrary command execution on the system. Exploitation evidence was first observed by the Shadowserver Foundation on 2026-03-31 (UTC). Added CVSS V4.0 AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-306 Added Reference https://h4cker.zip/post/d5d211/ Added Reference https://ti.qianxin.com/vulnerability/notice-detail/1760 Added Reference https://www.vulncheck.com/advisories/weaver-e-cology-unauthenticated-rce-via-dubboapi-debug-endpoint Added Reference https://www.weaver.com.cn/cs/securityDownload.html#